Port knocking is a technique that you can use to protect from Brute Force attacks. What it does exactly, it will knock the MikroTik router in a similar way when you go to a visit to your friend, and you knock his house’ door. In case your friend opens the door for you and invite you to enter, then you can go inside his house, otherwise you will stay outside.
Same thing with port knocking on MikroTik router, you will have to knock on the MikroTik router on a port that you define. In case this is successful, then you can do Winbox, ssh, telnet, etc… to the router.
Let me explain it in a better way. Say that you want to allow, from the WAN, access to the MikroTik router only via Winbox using port knocking. Then you need to create some filter rules doing the following:
- First rule: any device coming to the WAN interface as TCP port 1111 (you can define the port that you want), then add its IP to an address list (called Pnock1) for 10s.
- Second rule: if the same device (meaning same source IP) has tried to do a connection on the WAN interface of the MikroTik router as TCP port 2222 within the 10s, then add its IP to a new address list (called Pnock2) and leave it there for 30 min.
- Third rule: in this rule you will say that any IP which is inside the 2nd address list (Pnock2), is allowed to do Winbox to the router.
- Fourth rule: in this rule, you just drop any input traffic to the MikroTik router coming on the WAN interface.
Doing those rules, only people who know the right destination TCP ports (1111 and 2222) can do the port knocking and able to connect via Winbox on the MikroTik router (if they have the right username and password), otherwise all other input traffic to the WAN interface will be blocked.
This is how the port knocking works, let’s apply that in a LAB and see if it will work for us.
LAB: Port Knocking
Now we know the theory behind port knocking, let’s do a LAB to see if it will work for us.
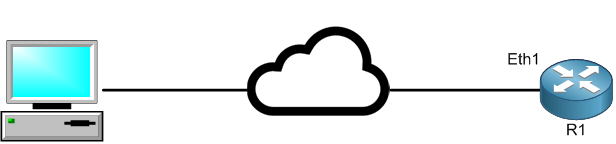
I have here a PC which is able to reach R1 via the internet. I want to configure port knocking on R1 in a way that only users can login to the router via Winbox after the port knocking is successful.
I have to create the 1st filter rule on the MikroTik router saying that any traffic coming to the router itself as TCP on port 1111, then add the IP address of the source in an address list called “Pnock1” and leave it for 10s. Let’s do that:
Apologies, the Full Lesson Access is Only for Members....

Get Access to all Lessons from different Vendors
Affordable Price to Enhance your IT Skills!
Always Accessing all Lessons including the New Added Ones

100% Satisfaction Guaranteed!
You can cancel your membership at anytime.
No Questions Asked Whatsover!

0 Comments