MikroTik RouterOS is a stateful firewall. A stateful firewall is a kind of firewall that keeps track and monitors the state of active network connections while analyzing incoming traffic and looking for potential traffic and data risks. This firewall is situated at Layers 3 and 4 of the Open Systems Interconnection (OSI) model.
As MikroTik RouterOS is a stateful firewall, then it keeps tracks of opened connections such as ICMP, UDP, TCP, etc….
That makes the MikroTik RouterOS a great firewall device because, in contrary of the stateless firewall that do not inspect traffic and does not examine an entire packet, it can keep track of every connection that is opened, and it examines all packets which belong to those connections.
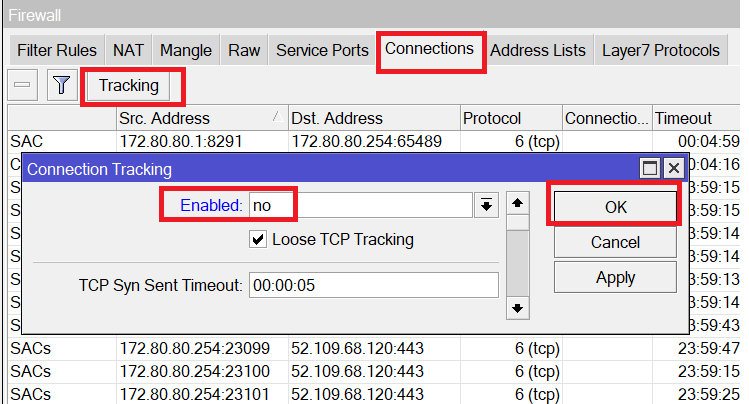
To show you that the MikroTik RouterOS is a stateful firewall, we can just look to the “Connection Tracking” tab inside the firewall:
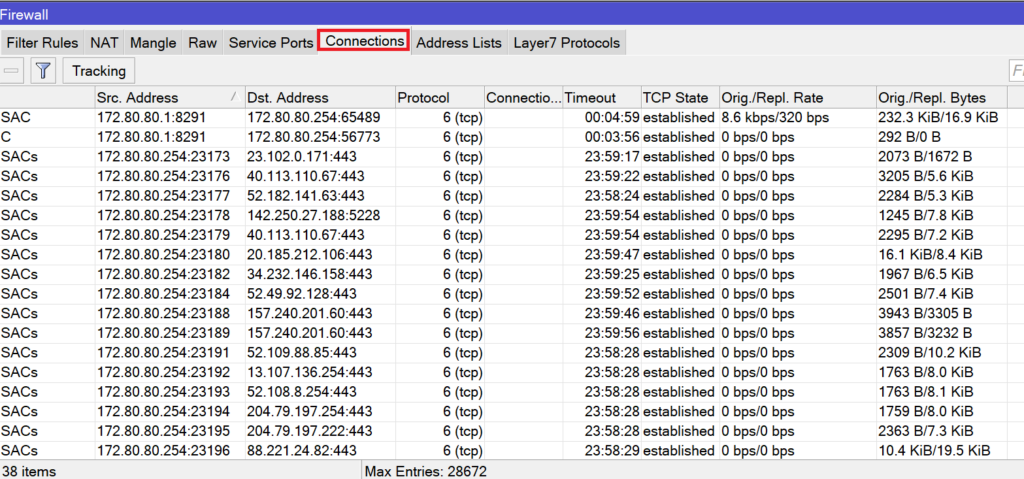
You can see, the firewall is tracking every connection that it opened on the MikroTik router.
This connection tracking can be disabled, but if you disable it then many features in the firewall will be affected such as:
- NAT
- firewall:
- connection-bytes
- connection-mark
- connection-type
- connection-state
- connection-limit
- connection-rate
- layer7-protocol
- new-connection-mark
- tarpit
How to disable the connection tracking? it is very simple, let me show you:
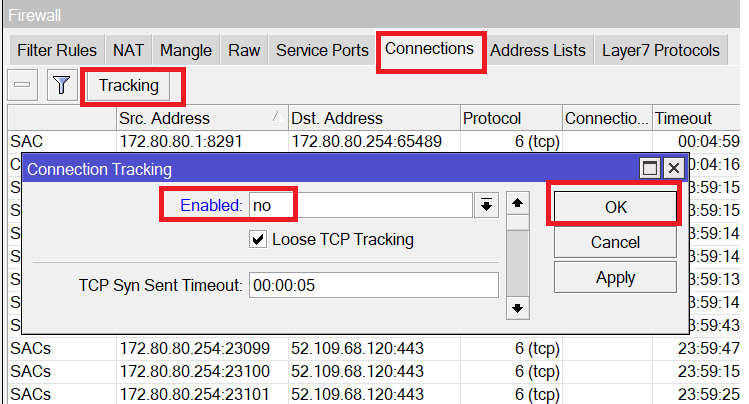
By doing that, the NAT will not work anymore, so what I was able to see as entries on the connection tracking will have to be wiped completely (those were NAT entries):
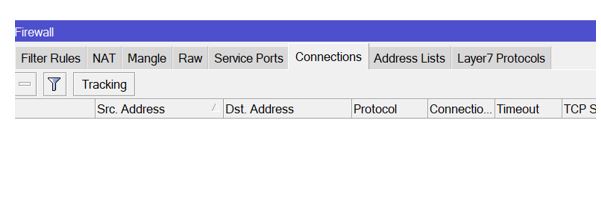
Everything is gone, and now no one from the inside LAN will be able to go to the internet because the NAT is not functional ☹
LAB: Stateful Firewall
Here is my LAB scenario. I have configured R1 to be connected to the internet and sharing the internet to my PC. So R1 has NAT enabled to allow my local PC to go to the internet.
Let’s check 1st if my PC can ping google DNS:
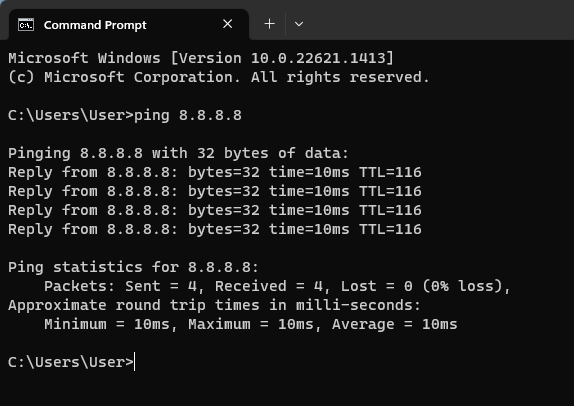
Indeed, it can.
Just for fun, let me disable the connection tracking and see if my PC will be able to ping google DNS again:
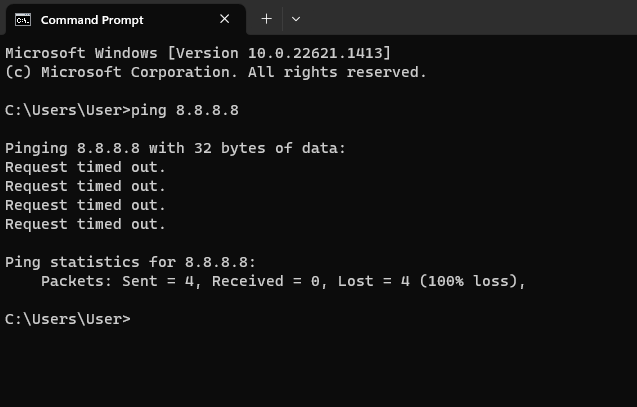
I see clearly that I cannot ping to google DNS anymore, and that’s because once you disable the connection tracking then many firewall features will be stopped including NAT.
Now I just want to show you that the Firewall on the MikroTik RouterOS is a stateful one.
After I have re-enabled connection tracking, I need to mark any ping connection going from my PC to 8.8.8.8 and give it a label, then I want to see if I can see that particular connection inside the connection tracking entries. This way I know that my router keeps tracks for all connections passing through the router.
To mark a connection, I will be using the mangle rule in the firewall. I will have to mark the connection that is trying to do ping to 8.8.8.8 and coming inside the interface Ether2 of the MikroTik router which is connected to my PC. Meaning that if my PC is trying to do ping to 8.8.8.8 then it will make the connection with a label.
Let me show you how to do that:
Apologies, the Full Lesson Access is Only for Members....

Get Access to all Lessons from different Vendors
Affordable Price to Enhance your IT Skills!
Always Accessing all Lessons including the New Added Ones

100% Satisfaction Guaranteed!
You can cancel your membership at anytime.
No Questions Asked Whatsover!

0 Comments