MikroTik RouterOS has services which are enabled always by default. Those services have ports assigned to them and they can be a way for the hackers to attack our router through them. For this reason, it is always recommended to disable the non-important ones, and to change the port numbers of the ones that we want to use.
What are those services, where we can find them and how to manipulate them? All of those questions will be answered in the upcoming LAB.
LAB: Managing RouterOS Services
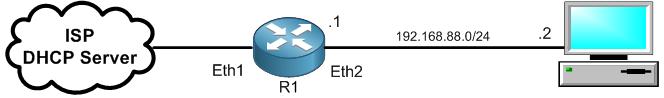
We are still in the same LAB scenario. Let’s check directly what are the services that I was talking about:
Apologies, the Full Lesson Access is Only for Members....

Get Access to all Lessons from different Vendors
Affordable Price to Enhance your IT Skills!
Always Accessing all Lessons including the New Added Ones

100% Satisfaction Guaranteed!
You can cancel your membership at anytime.
No Questions Asked Whatsover!

0 Comments