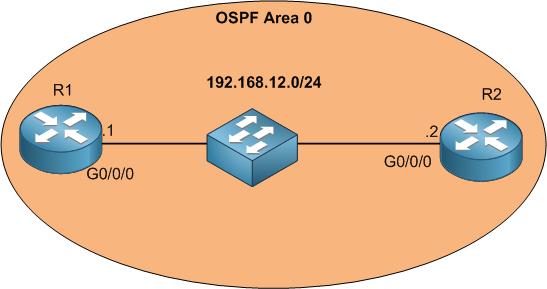
We are still in the same LAB. At this moment neighborship is formed between R1 and R2. We have seen in the hello packet that authentication on OSPF should match in order for the neighborship to be formed. By default, Huawei routers do not have any authentication on OSPF. This can cause a security hole because if anyone plug a router on the switch and configure OSPF then he can be a neighbor to our production network. For this, authentication is very important.
On Huawei you can configure authentication on area level or on interface level as following:
- Area authentication: the authentication will be applied to packets received by all interfaces in the OSPF area.
- Interface authentication: the authentication is configured on the interface level and is applied to all packets received by only this interface.
Apologies, the Full Lesson Access is Only for Members....

Get Access to all Lessons from different Vendors
Affordable Price to Enhance your IT Skills!
Always Accessing all Lessons including the New Added Ones

100% Satisfaction Guaranteed!
You can cancel your membership at anytime.
No Questions Asked Whatsover!

0 Comments