Also, another feature on Layer2 Security is called Port Security. Let’s say that on Ether2 port we have a PC connected and we don’t want any other device connected to this port to work but my own PC. Then I can apply Port Security from which only the MAC address of my PC is allowed to be passed and any other MAC address is not allowed.
LAB Port Security:
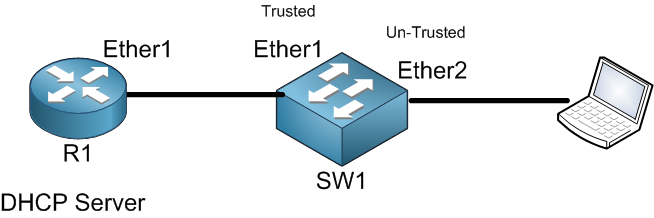
Still on the same LAB scenario. I want my PC only to be allowed to pass from Ether2 of SW1 and anything else not able to.
First, we need to take the MAC address of the PC and save it:
Apologies, the Full Lesson Access is Only for Members....

Get Access to all Lessons from different Vendors
Affordable Price to Enhance your IT Skills!
Always Accessing all Lessons including the New Added Ones

100% Satisfaction Guaranteed!
You can cancel your membership at anytime.
No Questions Asked Whatsover!

0 Comments